Cisco SD Access: Scalable Group Tags
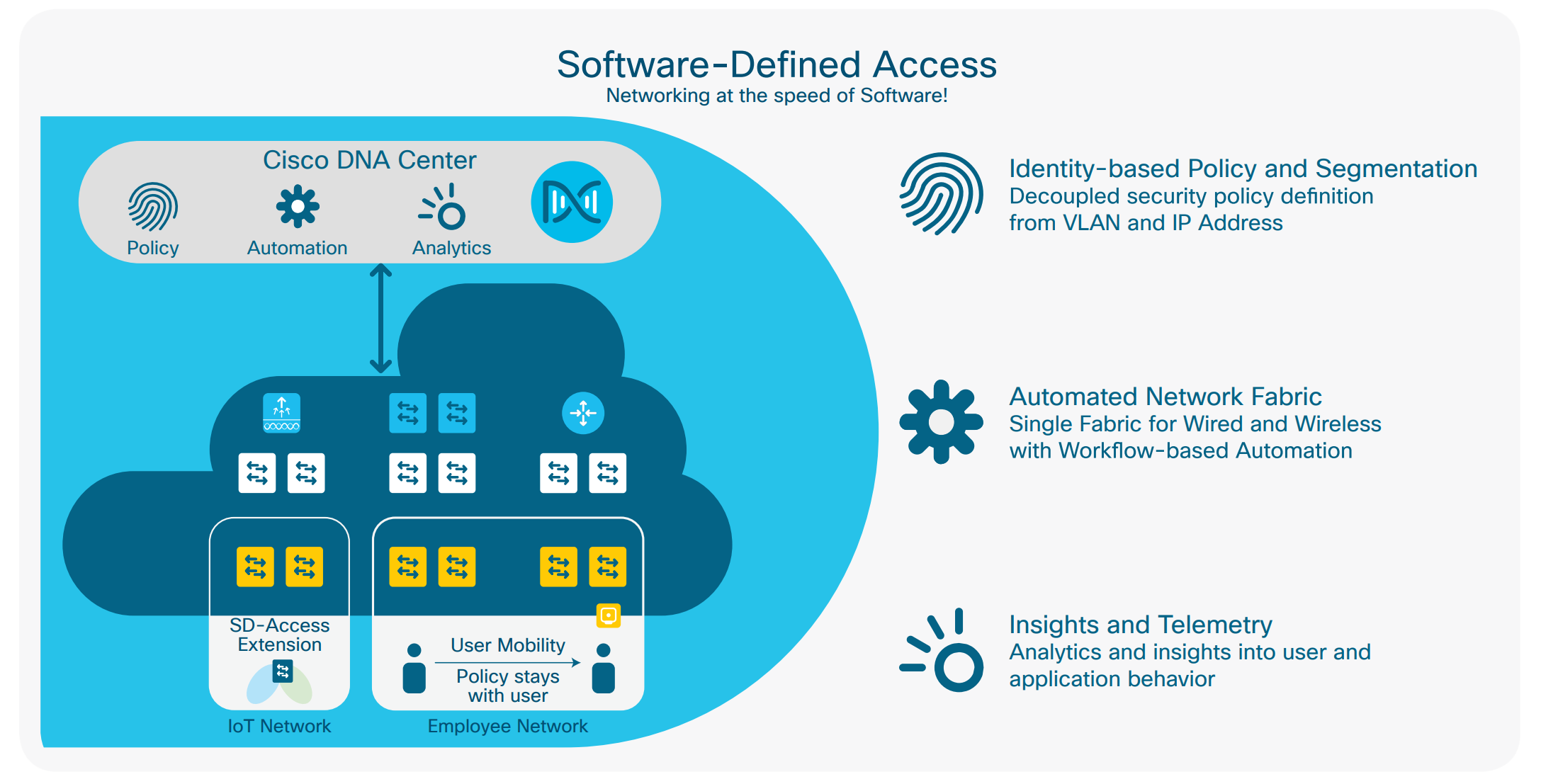
One of the Cisco Digital Networking Architecture corner stone concepts is Software Defined Access (or simply, SD Access). One of the key components is the use of Scalable Group Tags (SGTs) and these form a cornerstone of the SD Access story.
I've written a companion blog to this one, which explains the basics of Software Defined Networking, in the context of Cisco SD Access.

Introduction
In this blog, let's take a look at the subject of Scalable Group Tags in the context of SD Access.
.gif?width=189&name=Deploying%20Cisco%20SDA%20(Instagram).gif) The message I have been receiving from Cisco is that SDA is the (only) way that we should be designing our future networks.
The message I have been receiving from Cisco is that SDA is the (only) way that we should be designing our future networks.
To me that seemed like a bitter pill to swallow because one had to admit that the current practices were no longer valid, and failure to adopt this paradigm shift would result in certain doom.
I have though had a breakthrough moment around the subject of SDA and why we should care about it.
I would caveat this by saying that the world won't end if we didn't all adopt SDA - but there are real advantages to be had if we adopted this new way of thinking.
We have a wealth of other articles, if you wanted a quick refresher on the topic of Software Defined Networking.
Associated Blogs:
- Cisco SDA
- Cisco SD Access: Micro Segmentation Explained
- Top 5 Unique Features of Cisco ISE
- 5 Ways DNA Center Solves your Challenges
What is SD Access
So, here is my SDA elevator pitch from an engineer's perspective:
- SDA creates a network layer over the top of your existing network to allow the easy distribution of SGT's.
The more correct terminology is that SDA is an overlay technology that sits on your underlay (your existing network).
ASSOCIATED BLOGS:
- Cisco SD Access: Micro Segmentation Explained
- How to Build an SDA Fabric Lab: Part 1
- How to Build an SDA Fabric Lab: Part 2
From TrustSec to Scalable Group Tags
The adoption of CTS (Cisco TrustSec) over the last ten years has not been very far reaching, but first a quick reminder of what TrustSec is:
- TrustSec: Is a framework that made Network Segmentation easier by assigning Tags to traffic, and to treat that traffic based on Source and Destination Tags, as opposed to Source and Destination IP addresses

This distinction of a traffic stream is crucial, because IP addresses are hard to deal with and one user may appear in numerous IP Source Addresses, thus making ACL's very complex.
SGT (Scalable Group Tag) is the name given to the tags attached to these traffic streams, and they can convey more than just Security (as their initial acronym of Security Group Tag suggested).
Quick reference on what makes a SGT scalable are the uses for the tag::
- Security
- QoS
- .. and many other uses
ASSOCIATED BLOG:
- Cisco SD-Access Lab
- DNA Center Beginners Guide
- Cisco DNA Center Enablement
- Cisco DNA Spaces Introduction
It's also an IETF standard
I would wager that one of the top reasons for the low acceptance of TrustSec in the market , is that customers don't always have the right hardware in place to support TrustSec.
Many years have gone by since Cisco announced TrustSec, and the discussion often centered around device compatibility to support inline tagging or SXP (SGT Exchange Protocol) support.
There used to be issues with SGT not being supported on many devices.
SDA solves that problem because SGT's no longer get involved in the underlay. Problem solved.
The overlay however still needs to deal with SGT's and this is done by fewer, and more strategic devices in the network. The overlay is also referred to as the Fabric.
ASSOCIATED BLOGS:
Cisco SD Access Demystified: Final Thoughts
SDA is a real thing and it is finding its way into customer networks. It's probably the most significant development from Cisco since the advent of MPLS almost 20 years ago.
It's interesting to note that Cisco also invented Tag Switching 20 years ago, which later became standardised as MPLS Label Switching and was widely adopted. SDA relies on standards based protocols like LISP, IS-IS and VXLAN.
Scalable Group Tags are the underlying mechanism, with the aim being to enable the Macro and Micro Segmentation feature.
It can sound like an acronym soup at times, but the more you immerse yourself in this topic, the clearer it will be.
ASSOCIATED BLOGS:
.png?width=200&height=59&name=IPTellogo-byline-2020-dark-v2-pnd-optimised-500%20(1).png)