Cisco SD Access: Micro Segmentation Explained
In our series of blogs exploring Cisco SD Access, we took a look at What is SDA Fabric as an overview. In this blog we'll dig deeper and take a look at the concept of Micro Segmentation. Micro Segmentation is all about providing a level of granular network control never seen before. Let's take a look.
I've written a companion blog to this one, which explains the basics of Software Defined Networking, in the context of Cisco SD Access.
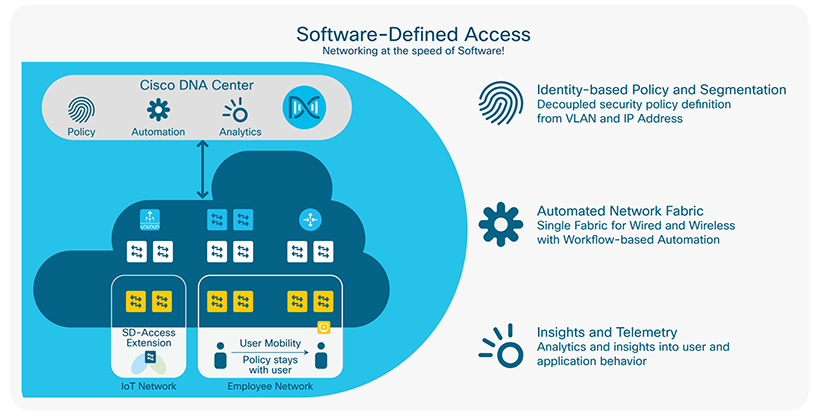
There are a number of components which make up the Cisco SD Access story. Cisco DNA Center is a fundamental component, along with SD Access capable network equipment.
ASSOCIATED BLOG:
- DNA Center Enablement
- Zero Trust Architecture (ZTA) Introduction
- Zero Trust Architecture (ZTA) Deployment
- The CIOs Guide to Cisco SDA
Introduction
We have a wealth of material around the topic of Software Defined Networking, so feel free to have a look through our other blogs.
.png?width=185&name=What%20is%20Cisco%20SDA_%20(Instagram).png) SD Access opens up a world of possibilities for networking, and one of these is these is to deploy a highly granular security architecture.
SD Access opens up a world of possibilities for networking, and one of these is these is to deploy a highly granular security architecture.
Scalable Group Tags (SGTs) allow for the ability to provide a level of control not previously available in a layer 2 network architecture, and are a key concept in the deployment of Macro and Micro Segmentation.
Let's take a deeper look.
ASSOCIATED BLOGS:
Macro and Micro Segmentation
There's a few concepts to run through to explain Macro and Micro segmentation. The first is Cisco SD Access Fabric. Fabric is a base network architecture which in essence is the transition from our beloved CLI to the automation of the GUI.
.png?width=185&name=Deploying%20Cisco%20SDA%20(Instagram).png) The fabric has another benefit over and above a regular design that may already be using SGT's - and this is the inclusion of Virtual Networks (VN's)
The fabric has another benefit over and above a regular design that may already be using SGT's - and this is the inclusion of Virtual Networks (VN's)
VN's are in essence the same thing as VRF's (Virtual Routing and Forwarding) that we know from MPLS and VRF-Lite in the Enterprise.
VRF's have been used for a long time to logically separate parts of the network that need to be kept separate.
If you have ever tried to stitch together an Enterprise campus using VRF-Lite, you'll know the pain that was involved there - it was not trivial.
Now, imagine a VN for Students, Staff and Guests - users in each VN are isolated from each other and need to be explicitly allowed to inter communicate. Okay, but what are SGT's used for then?
SGT's are the Micro-segmentation lever in SDA. They allow us to further sub-divide the class of endpoints in a VN. For example the Biomedical VN might contain sensors, pumps and temperature probes - each type can be assigned its own SGT.
ASSOCIATED BLOGS:
Cisco VXLAN
So - let me re-iterate the point of SDA in a more technical level. In a word, it's VXLAN.
SDA allows the transportation of VN and SGT information through the network through the VXLAN header in the IP frame.
Here's a Cisco illustration of this, showing the original L2 frame embedded in the VXLAN frame:
The IP frame travels through your WAN, LAN, or multi-vendor network (unaware of all of this). That in essence is the power of SDA. It's an Overlay technology that enables a lot of cool features.
ASSOCIATED BLOGS:
Fabric Components
In SDA we interface with the fabric in two places:
- Fabric Edge: Clients/APs connect here
- Fabric Border: Exit point to the DC or WAN.
SDA Fabric is a term used to describe the entirety of the network automation solution. One of the most important pieces of SDA is the Controller.
This is not to be confused with an SDN controller that constructs the individual IP flows, but rather, the SDA controller is a Cisco device that maintains the IP Address to SGT/VN mappings in a database and the uses the LISP protocol.
The Controller can be deployed in various sizes and of course in High Availability. If the Controller Function were to fail entirely, then it would not stop user traffic from flowing, but it would prevent new LISP communications from being established.
ASSOCIATED BLOGS:
Cisco SD Access Micro Segmentation: Summary
This and other blogs on the IPTel website take a look though the array of topics on the subject of Software Defined Networking.
The concept of SD Access is to provide an automated network deployment, less prone to human error and faster, quicker and cheaper to deploy.
Along with the base aims comes an array of useful other features - the ability to provide much more granular and simplistic control of device access is the aim Micro Segmentation.
ASSOCIATED BLOG:
.png?width=200&height=59&name=IPTellogo-byline-2020-dark-v2-pnd-optimised-500%20(1).png)