Cisco SDA Fabric Key Concepts
Software Defined Architecture is the concept that we can configure the network from a centralised management system. In the case of Cisco, this is DNA Center.
SDA removes us as engineers from the CLI configuration layer, although the physical layer still needs careful design in order to ensure no single points of failure and that the physical design is resilient.

SDA applies two concepts to the network configuration:
- Underlay: The network will configure blank switches, with full layer 3 and uses IS-IS to route between
- Overlay: The network will configure Policy Contracts on top of the underlay to provision the actual end user experience
ASSOCIATED BLOG:
LAN Switching: Key Fabric Concept
There’s a pretty interesting concept which is applied to the use of Fabric in a LAN switching scenario.
While you configure the IP ranges to be used, the network applies the underlying VLANs, so you no longer have to worry about that side of the Layer 2 design (in fact its all somewhat redundant now, since the move is to Layer 3 route, even at the access layer).
The essential concept then is the ‘exploded switch’. This is that once Fabric is enabled, all switches really operate as one giant switch.
Think of the normal 3 layer Cisco switching hierarchy – you have all those access switches, but now they are treated a one large switch – plug in wherever you like and get the same user experience.
ASSOCIATED BLOGS:
Cisco DNA Center

Cisco DNA Center is really at the heart of the SDA Fabric story.
DNA Center is the management platform for SDA, and so a key pre-requisite is to install DNAC first.
This allows you to start with Assurance mode on your existing network, moving to full Automation (configuration) mode on the new network.
DNA Center Enablement is a key aspect of the whole SDA Fabric deployment and should be integrated as a first stage in your plans to deploy SDA Fabric.
ASSOCIATED BLOG:
SDA Lab Environment
Building a lab environment is well worthwhile at the start of your SDA Fabric journey. This will allow you to test out key concepts, as well as refine the way in which your change controls and actual implementation will operation.
We've got a two part series of blogs on how to build an SDA Fabric Lab:
WLAN and Fabric
The design and configuration of a wireless LAN is not unaffected by Fabric. We have some new concepts to take a look at for the WLAN:
- Fabric Mode WLC: CAPWAP is still used – but traffic is not all centrally switched any longer
- Fabric Mode APs: Operate in local mode – use central CAPWAP for control and user traffic dropped off local
The image below details some of the key concepts for the SDA WLAN Architecture:
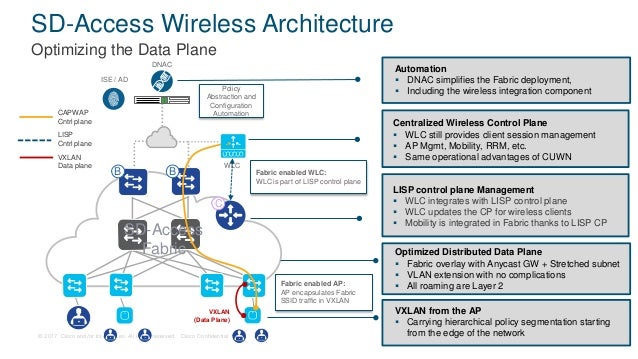
*Image from Cisco Connect Vancouver 2017
The way in which SDA works with regards to WLAN traffic is much more akin to the local mode switching, which is a current option.
This means that user traffic is dropped off locally at the AP and not shipped over the CAPWAP tunnel to the central WLC. The underlying SDA architecture is responsible for then ensuing that traffic can get to where it needs to go.
Under the surface, the AP forms a VXLAN connection to the access switch it is connected to. This then allows the use of policy(ies) to dictate how user traffic is treated, with the really important (new) operating mode: WLAN traffic is treated identically to wired traffic.
The applied policies affect and are applied to the WLAN traffic in an identical way to wired – as user traffic exits the AP and enters the LAN, it is essentially exactly the same as if traffic were deposited onto the LAN from a wired client. Micro Segmentation policies applied in exactly the same way to WLAN traffic as they would with LAN based traffic.
Final note – you’ll need to upgrade to at least AIROS code version 8.5, which will then allow your 9800 WLC to fully support SDA.
ASSOCIATED BLOGS:
- Cisco SD Access: Micro Segmentation Explained
- Troubleshooting with DNA Center
- Cisco DNA Center Assurance
- 5 Ways DNA Center Solves your Challenges
SDA Fabric Key Concepts: Summary
The primary concept to take away is that WLAN user traffic will be treated in SDA exactly the same as LAN traffic. From the minute that WLAN traffic enters the LAN, it will be ready for SDA policies to be applied and will allow for Micro Segmentation in the exact same manner that LAN traffic can be managed.
This is pretty interesting for a variety of reasons.
You can now build much more universal policies for your traffic and apply those much closer to the source. Micro Segmentation allows you to really closely carve up what access the WLAN users have based on the identity of the users, not just the traffic profile – massively powerful in allowing very specific network access.
The other key take away is that when SDA is enabled, the APs are using VXLAN under the surface – no longer do you need to plan a huge Layer 2 deployment, with lots of VLANs and so on – SDA takes care of that underlay config.
ASSOCIATED BLOG:
.png?width=200&height=59&name=IPTellogo-byline-2020-dark-v2-pnd-optimised-500%20(1).png)